The minimal, immutable core that provides only essential services: kernel, init system, and graphics. No user applications, no persistent data, no configuration drift. Protected by cryptographic integrity verification.
Container-based realms offer near-native performance for trusted workloads. Hypervisor-based realms provide hardware-level isolation for high-risk activities like malware analysis.
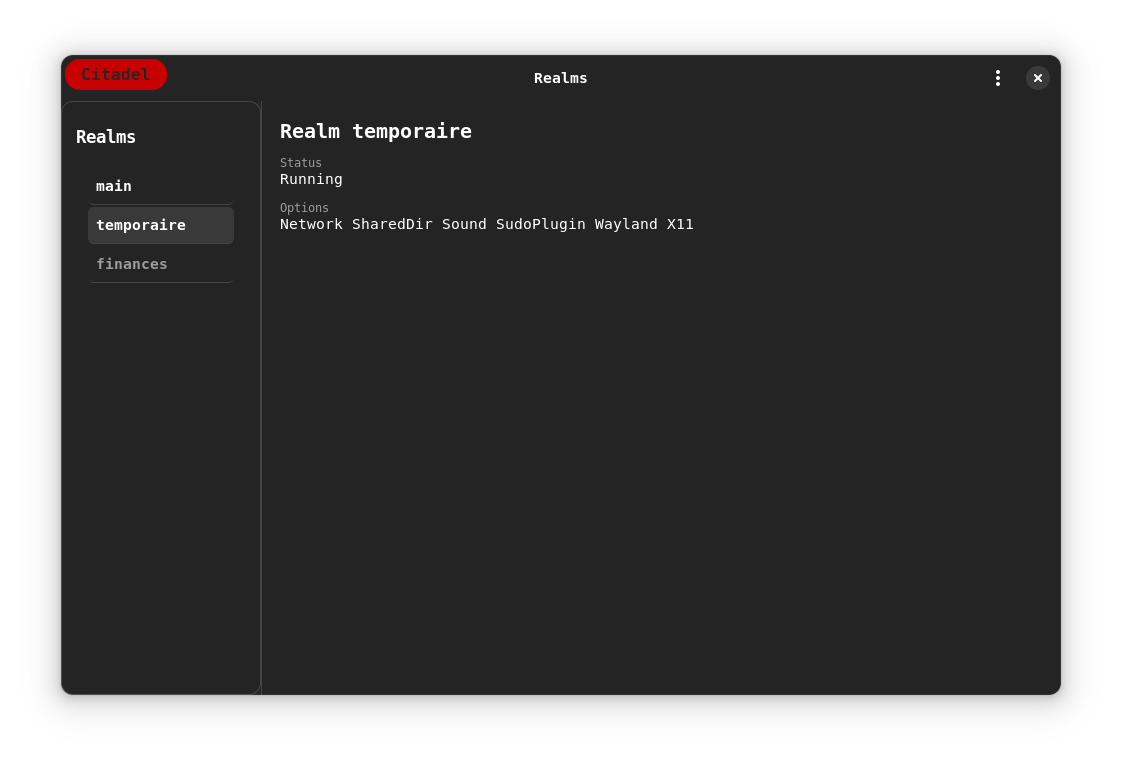
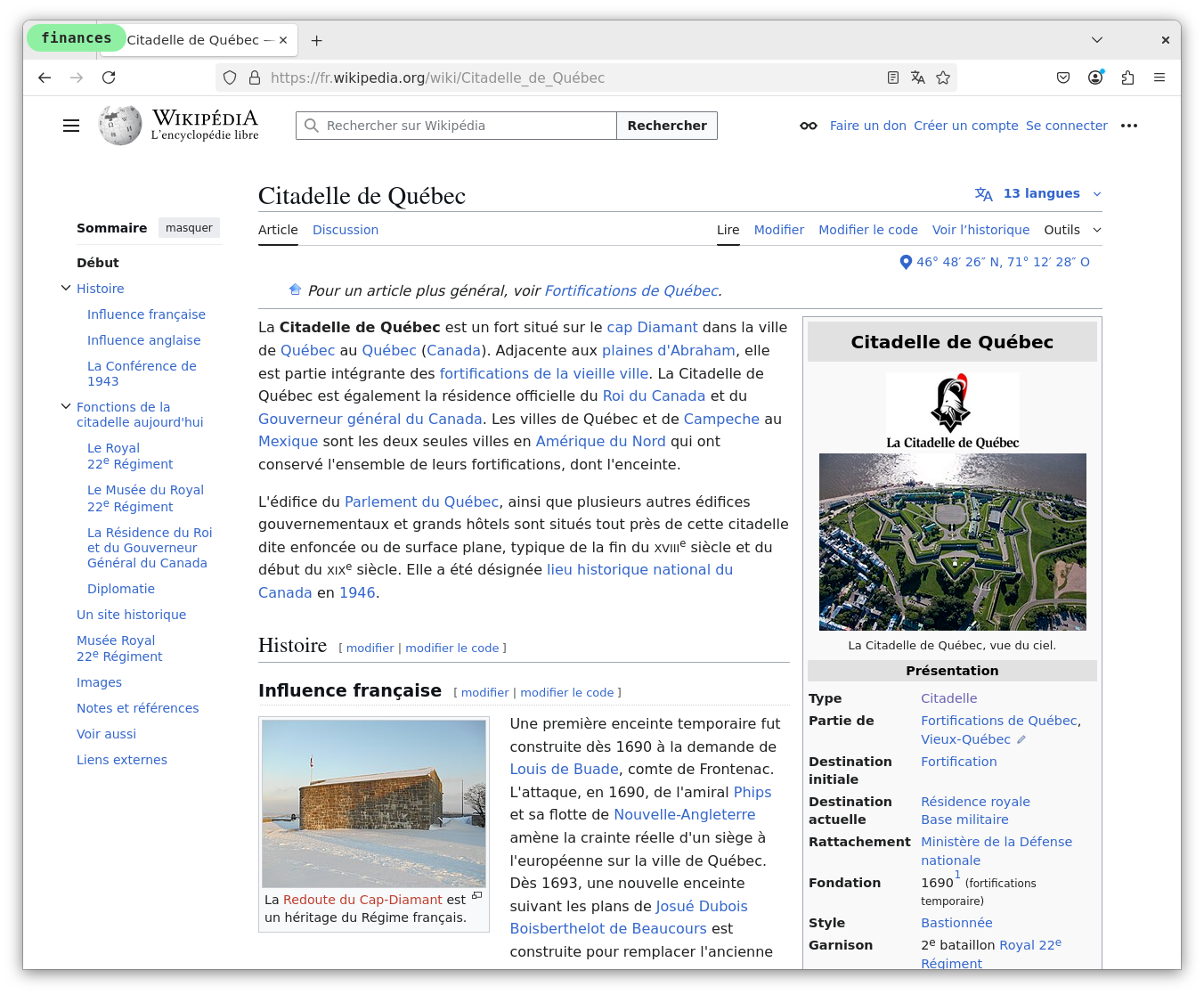
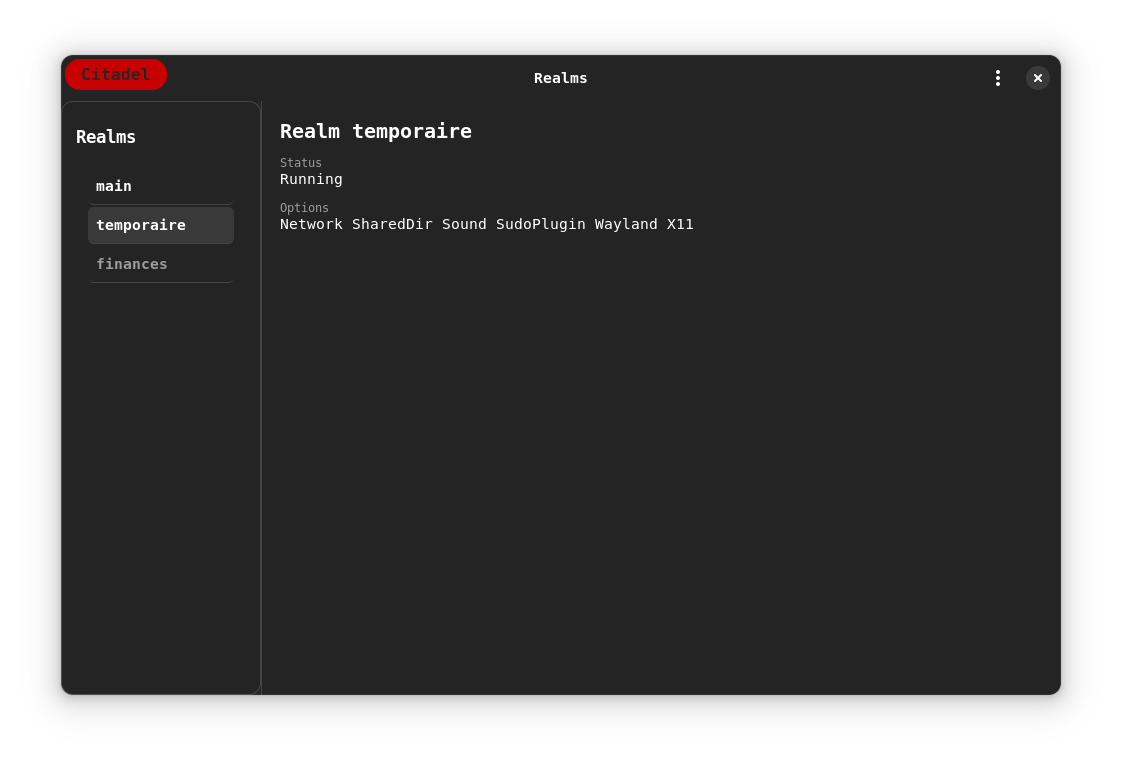
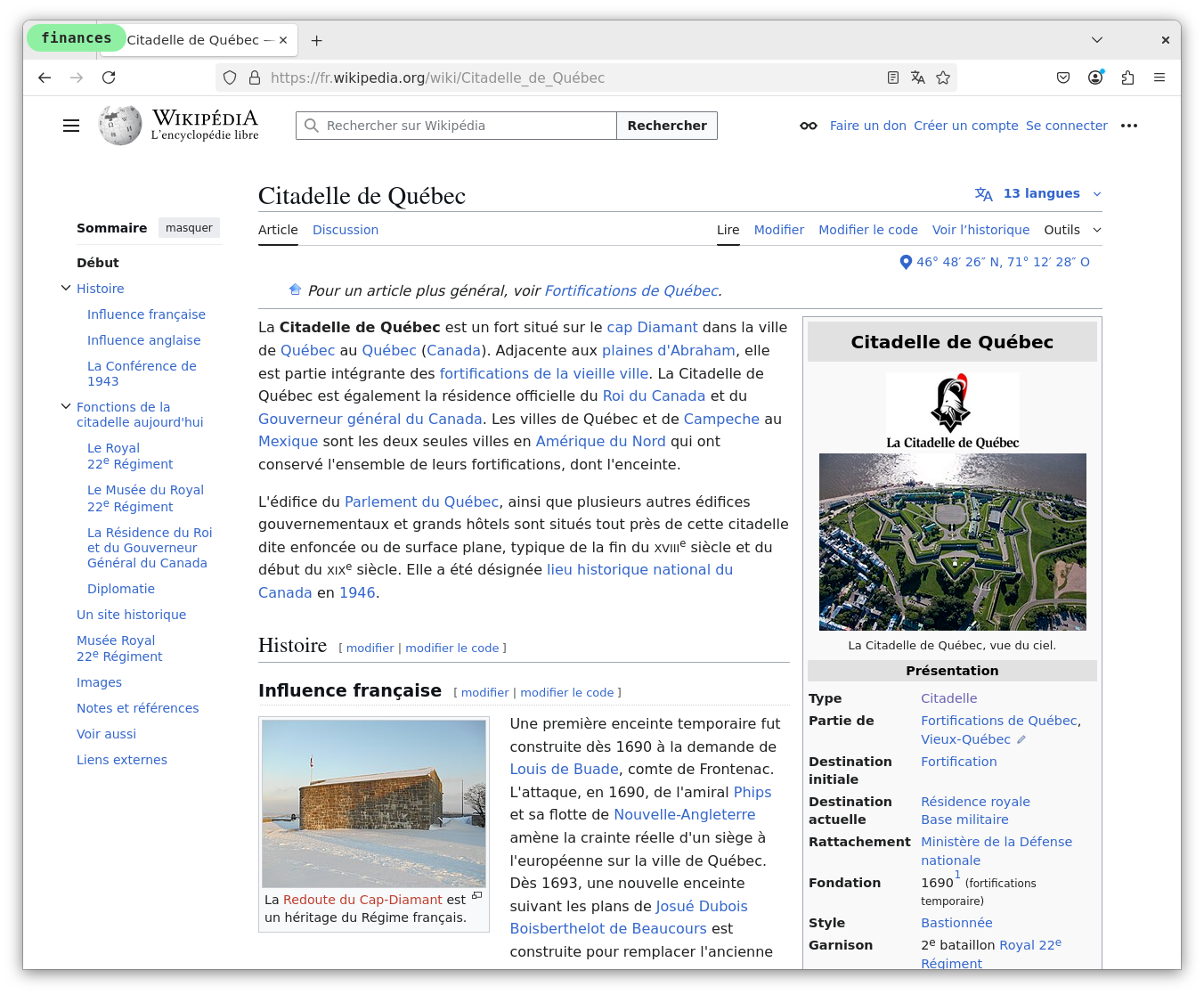
Completely isolated computing environments where your actual work happens. Each realm can only access its own data. Applications are read-only by default. Only user data persists across reboots.
Secure endpoints for privileged users at risk of targeted attacks
Isolated development environments without cross-contamination
Safe analysis environments for malware and vulnerability research
Secure workstations for executing sensitive financial transactions
Compartmentalized computing for classified and sensitive operations
Secure computing for vehicles, kiosks, and specialized hardware
dm-verity provides cryptographic verification of every block in the base filesystem. Any tampering prevents boot, ensuring a pristine starting state.
Complete process, network, and filesystem isolation between realms using kernel namespaces or hardware virtualization.
The core Citadel system is mounted read-only. No configuration drift, no persistent malware, no accumulated security debt.
UEFI Secure Boot through kernel loading ensures only cryptographically signed code executes during system startup.
Every binary can be independently verified to match the claimed source code, eliminating supply chain compromise.
TPM integration for cryptographic key storage and attestation. Hardware random number generation for strong entropy.
We’d love to hear from you. Please email us info@subgraph.com.